
Note from the Editor: This article shares highlights from an older report. For the latest on data security and best practices for keeping file transfers safe, visit our Data Security page or check out the latest additions to our blog.
The 2017 Cybersecurity Trends Report was recently released by Crowd Research Partners. The report covers many aspects of cybersecurity, such as general security trends, cloud and mobile security, and managed security services. It also looks at how organizations are securing their file transfers, including some common file security pitfalls.
Here’s what the Cybersecurity Trends Report has to say about file transfers.
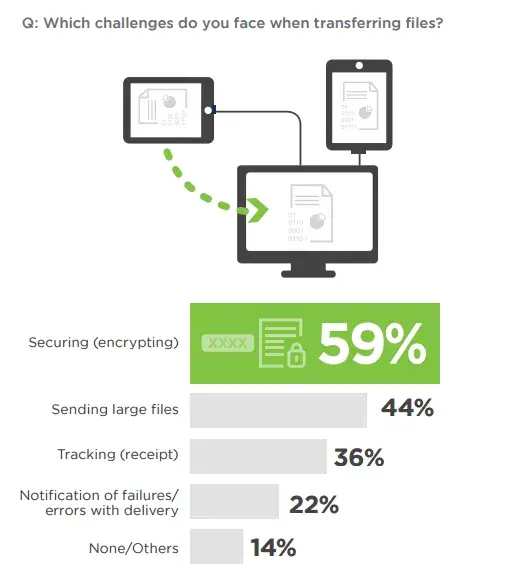
Security is the Top File Transfer Concern
When it comes to the challenges businesses face when transferring files, security is at the top of the list, with 59 percent of respondents citing it as a concern. Furthermore, over half of the IT security professionals surveyed said that if their file sharing practices were audited for regulatory compliance, they do not have the tools they need to streamline the process.
Managed file transfer (MFT) is the clear answer for both security and compliance challenges. A good MFT solution will provide a variety of encryption methods and secure protocols to combat modern data security threats. MFT software also includes detailed audit logging capabilities to ensure you can prove your file transfers are compliant in case of an audit.
Securing Customer Data is Critical
Protecting sensitive data is a significant concern for most organizations. Above all, companies are worried about the security of customer data—72 percent of survey respondents cited it as a type of sensitive data they are most concerned about protecting.
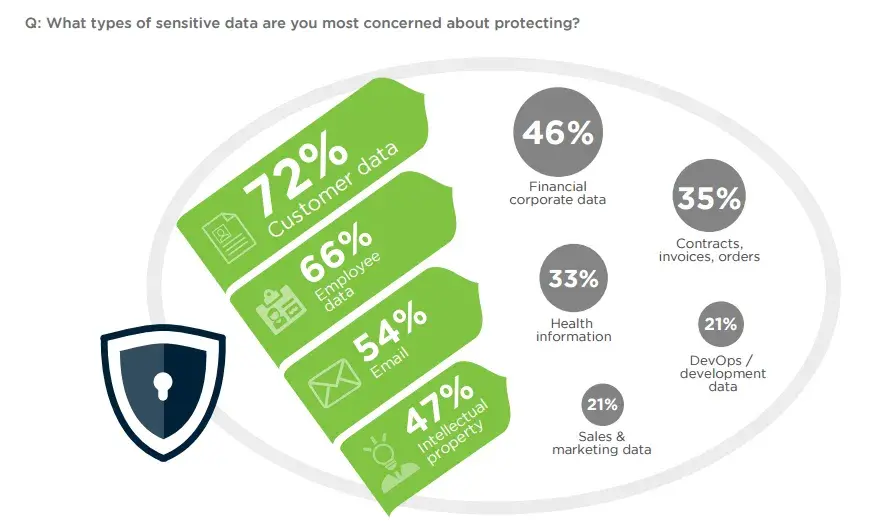
There’s good reason to be careful about customer data. According to Verizon’s latest PCI DSS Compliance Report, 69 percent of consumers would be less inclined to do business with an organization that had suffered a data breach. Customer data security is also essential for maintaining compliance with PCI DSS and other industry standards.
Other types of data that respondents are concerned about protecting include employee data (66 percent), email (54 percent), corporate financial data (46 percent), and health information (33 percent)—important if you need to comply with HIPAA.
A managed file transfer solution can provide end-to-end encryption to protect files at rest and in transit. 67 percent of survey respondents ranked encryption as the most effective means for protecting data.
Too Many Organizations are Using Inadequate File Transfer Methods
Email is still the most common file transfer method for smaller files, used by 63 percent of respondents. This is a serious risk as unsecured email is both vulnerable to cyberattack and difficult to track for auditing purposes. Another 18 percent rely on writing custom scripts, a method that is both time-consuming and prone to error.
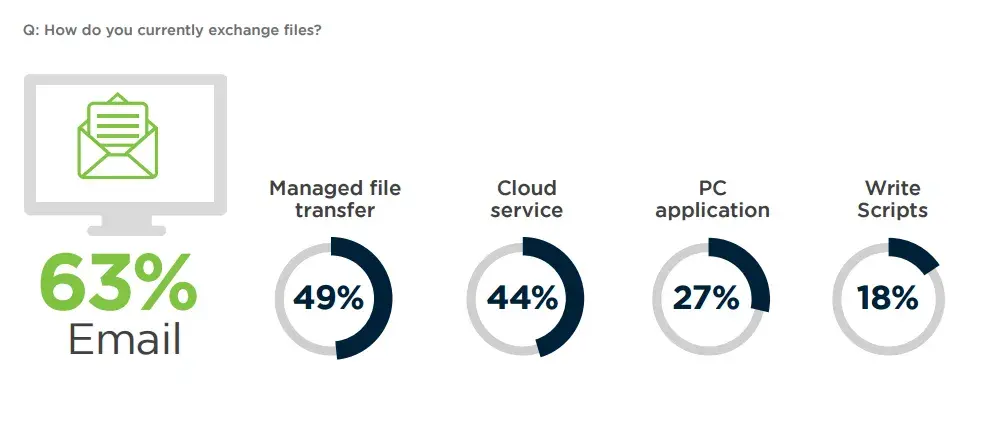
Fortunately, 49 percent of respondents have implemented managed file transfer software. Managed file transfer streamlines the secure exchange of data and provides organizations with a single point of control for all file transfers. Implementing an MFT solution that provides enterprise-level security features, role-based security, and full audit trails, is the best way to make sure your data transfers stay ahead of constantly evolving security threats.
To learn more, download the full Cybersecurity Trends Report (links to PDF).
