Create an SSL Certificate
Before configuring the HTTPS/AS2 service, it is first necessary to create an SSL certificate that will be used to protect the HTTP tunnel.
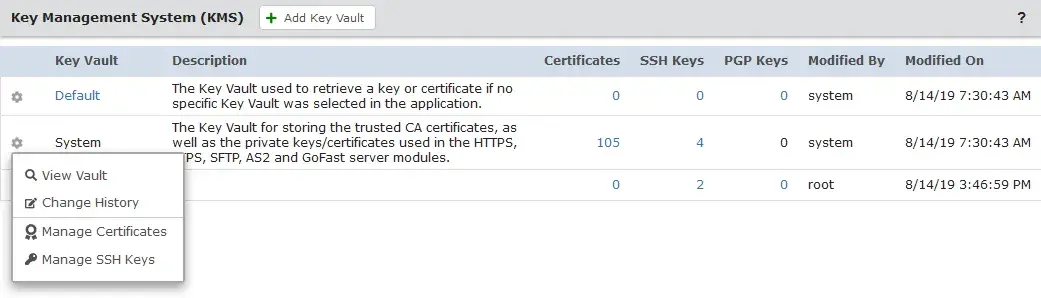
To create the SSL certificate, log in to GoAnywhere MFT. Click Encryption from the main menu, and then click the Key Management System link. Here you will find a list of Key Vaults. From this page, click on the action icon next to the System Key Vault and select Manage Certificates.
From within the Key Vault, you can import, create, or modify certificates. To create the new SSL certificate, click on Add Certificate. You will then need to complete the SSL Certificate form.
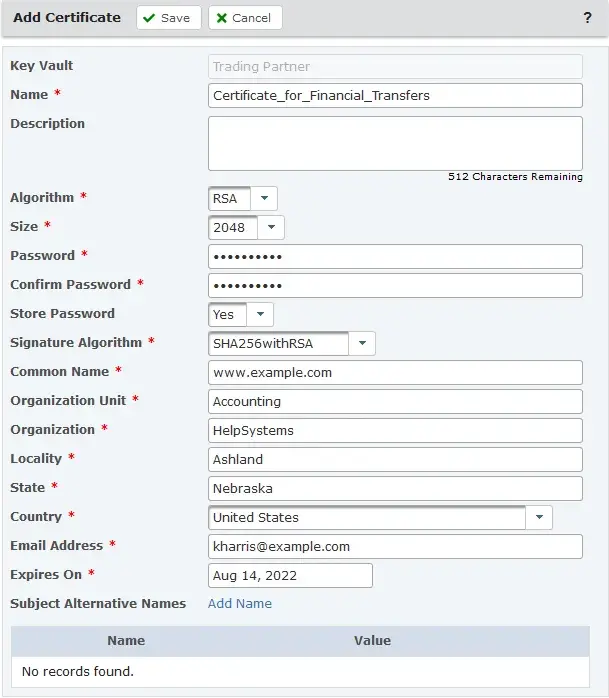
A few field notes:
When you are finished completing the SSL Certificate form, click Save, which will return you to the Key Vault.
Create a Signing Request
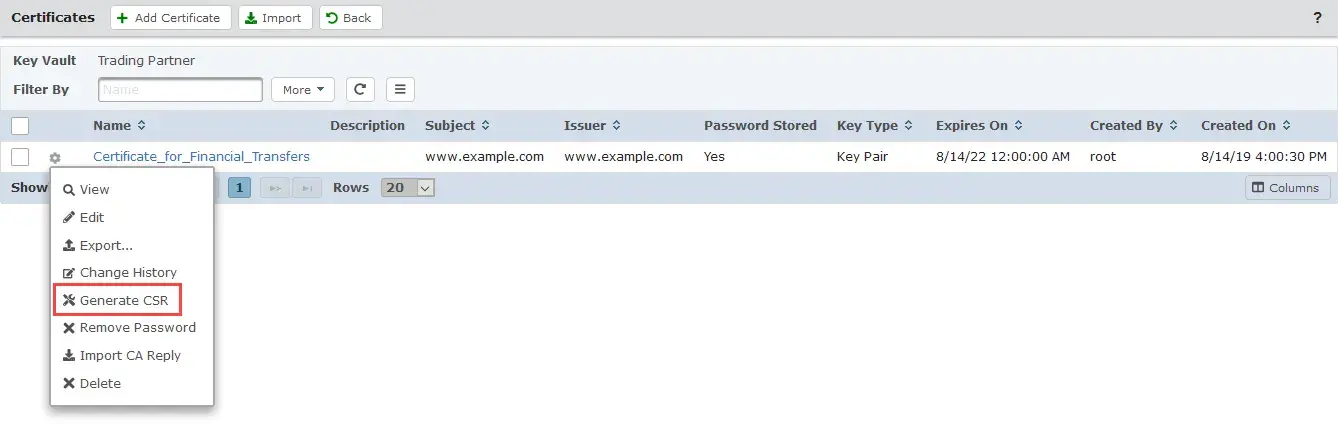
If you need a signed certificate, you’ll need to create a signing request for your Certificate that you will send to a Certificate Authority (CA). This is necessary if your trading partners require your Certificates to be signed by a CA and not self-signed.
Select the Action icon for the Certificate and then select the Generate CSR option. The file will download to your internet browser’s default folder. The file will be named using the Certificate’s Alias with a .csr extension. You can then send this file to a Certificate Authority (CA) for signing.
Importing a CA Approved Certificate
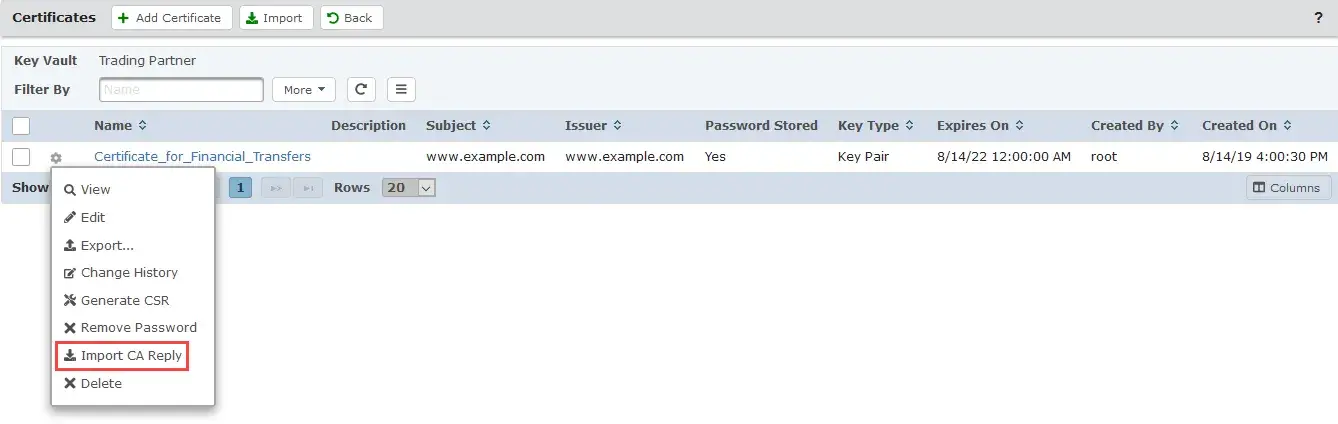
When your CSR is approved, you will receive a reply from your Certificate Authority that will contain an updated digital certificate. To import this certificate, return to the SSL Certificate Key Vault, select the Action icon for the Certificate and then select the Import CA Reply. You will be prompted to identify the location where the CA Reply file is located. Input the location or browse for the file.
It may also be necessary to import all intermediary and root CA public certificates into the key store to establish a trusted chain.
Assigning Your Certificate to the HTTPS Service
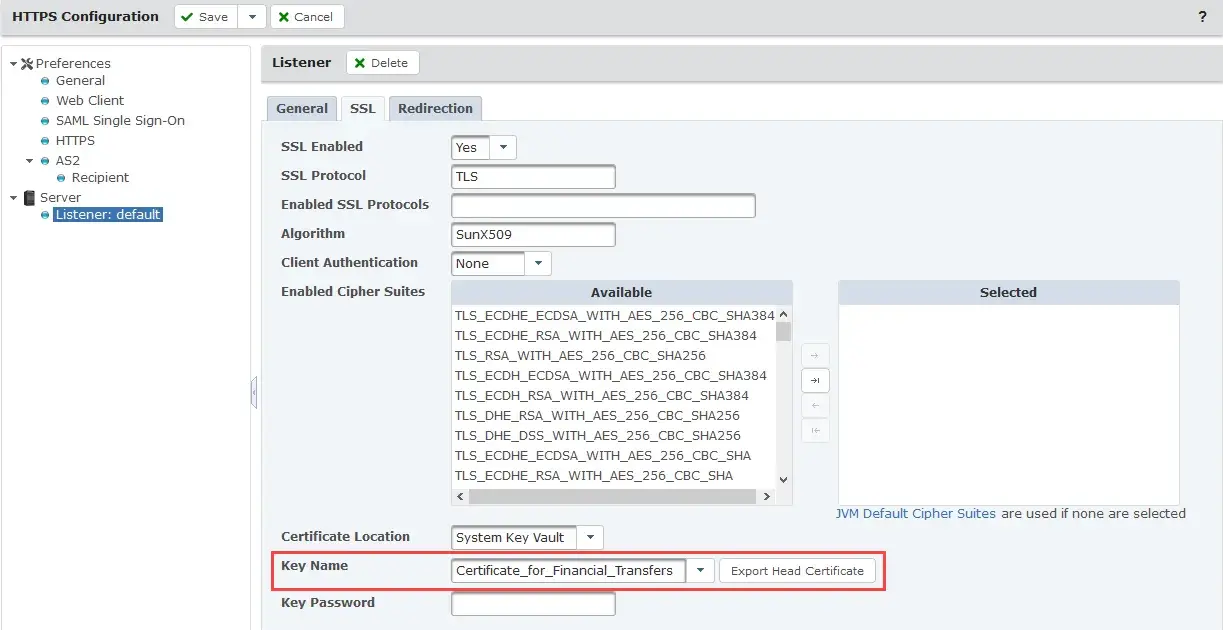
Now that your Certificate has been created and signed by a Certificate Authority, and the reply has been imported to your key store, you’ll need to assign the certificate to your HTTPS service. To do this, navigate to the Service Manager page via the Services drop-down menu. Once there, click the Action icon for HTTPS/AS2 Service and select the Edit option. On the HTTPS Configuration page, on the left-hand navigation pane, select Listener under the Server section.
In the Listener pane, navigate to the SSL tab. In the SSL tab, set the Certificate Location to System Key Vault. For the Key Name, select the name of the newly signed certificate. Once finished, Save and Finish your changes. Finally, restart the HTTPS/AS2 service by clicking on the Action icon and selecting Restart.