Exchanging files with both customers and trading partners is common, but keeping data secure during those exchanges can be a challenge. Finding the right solution can be difficult when you start to consider local and global compliance requirements governing data security, such as:
- PCI DSS
- HIPAA
- SOX
- GBLA
- GDPR
Companies often install file sharing services (for example, FTP/S, SFTP, HTTP/S servers) in a public zone for trading partners to access in order to protect internal/private networks. But when those servers and files leave the safety of the private network, companies risk exposing those services and data to outside attacks. That's where a DMZ security gateway in a network comes in.
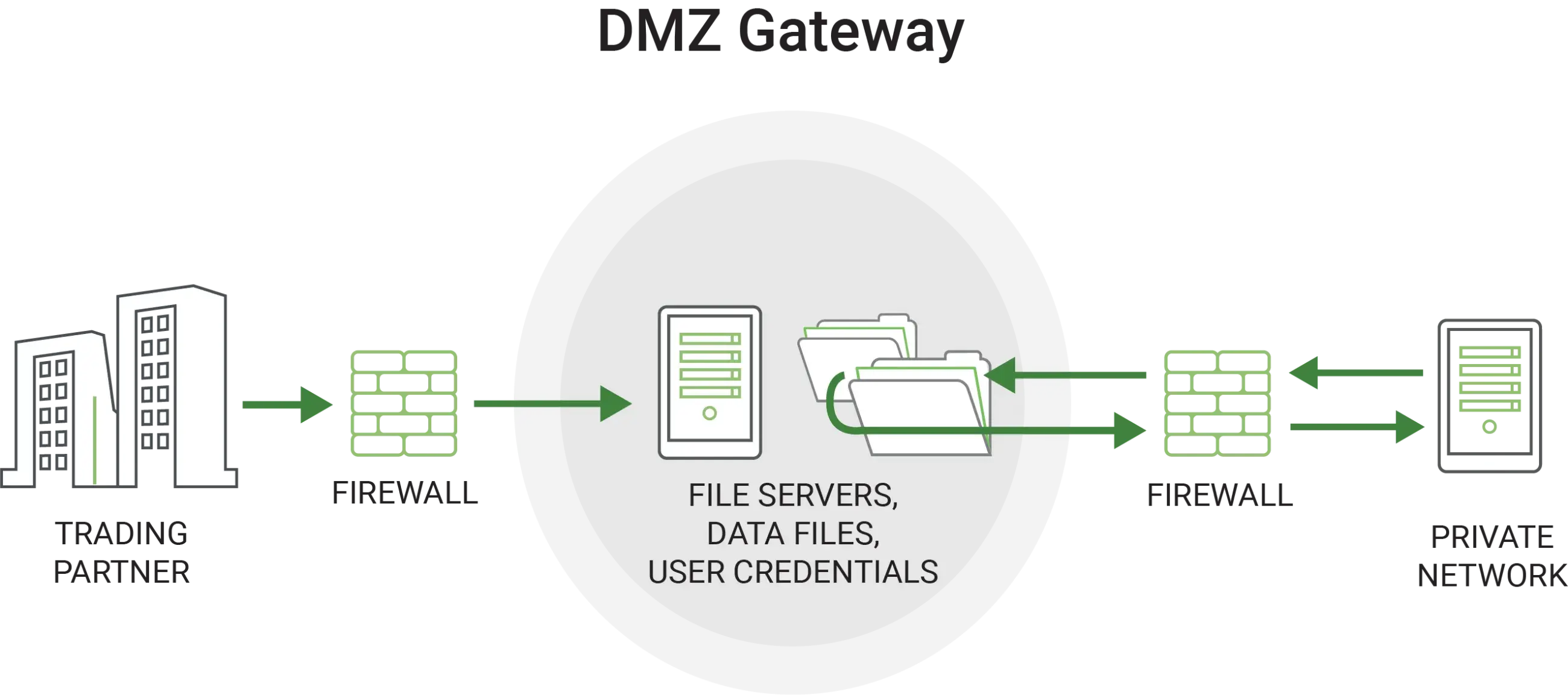
A DMZ acts as a buffer between internal data and outside forces much like a real-life Demilitarized Zone.
Complete the form on this page to learn more about how adding a DMZ secure gateway to your file transfer processes boost compliance readiness and can provide a critical layer of security between you and the rest of the world.
