
Are you using homegrown processes in your organization to send files on the IBM i? Between the knowledge required to write and maintain file transfer scripts, the time spent on creating user profiles for every file recipient, and the hassle of solving connection problems so data is always delivered successfully, manual IBM i transfers can be exceedingly complicated.
But they don’t have to be—as long as you have the right tool.
GoAnywhere Managed File Transfer (MFT) can save you time and effort on your IBM i systems. With comprehensive security controls, powerful encryption protocols, and limitless workflows, our MFT solution will help you reduce, if not completely eliminate, your need for complicated file transfer programs and procedures.
How does GoAnywhere MFT do all this, you ask? Keep reading to learn the ten ways it can improve your efficiency on the IBM i:
1. It Doesn’t Require Scripting or Programming Knowledge
With GoAnywhere MFT, scripting and programming can be things of the past. Use workflows instead of in-house processes to define and perform critical file transfers. Each workflow (or project) can contain a series of actions (called tasks) that perform specific processes when triggered. GoAnywhere includes 60+ built-in tasks, but you can also create custom tasks. Use them to send and retrieve data, encrypt and decrypt files, execute programs, provide status updates by text or email, and more.
GoAnywhere is also simple to deploy. It can run on-premises, in the cloud, or in a hybrid environment, with little to no technical knowledge necessary to get it working on your systems.
2. It Simplifies Key and Certificate Creation
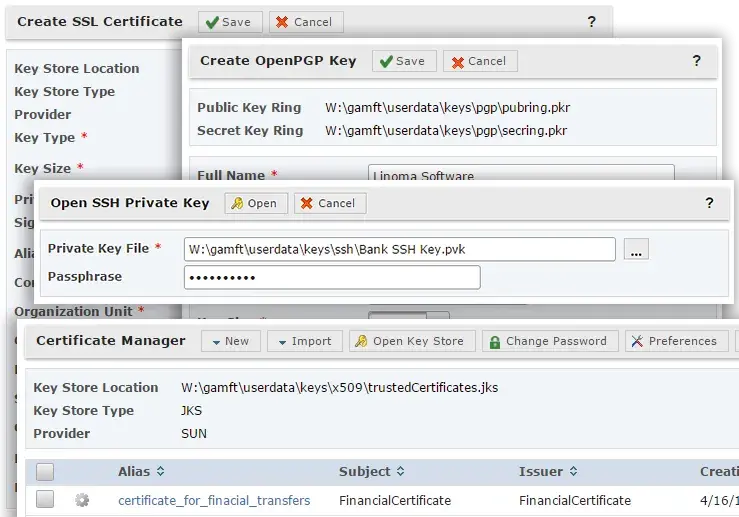
To generate keys and certificates on the IBM i, you need to use several commands, some of which are long and hard to remember. GoAnywhere MFT simplifies this process by allowing you to create and store whatever keys or certificates you need. All it takes is a few clicks of your mouse and absolutely zero commands.
GoAnywhere’s Key and Certificate Managers work with SSL certificates, SSH keys, and Open PGP keys. They’re accessible through the browser-based administrator interface and can be restricted to authorized users only. Need to send your public key to a trading partner? No problem. Importing and exporting keys and certificates in GoAnywhere is a breeze.
3. It Contains Comprehensive Security Controls for Your IBM i Data
Losing track of the security policies you have across your IBM i systems and looking for a better way to secure your data? Organize and manage certain aspects of IBM i security, as it relates to your files and IBM i information, with GoAnywhere’s comprehensive security controls.
Here is a sample of the security measures you can take in GoAnywhere to protect your data while it’s in transit or at rest on your IBM i systems:
- Create IP blacklists to block brute force and DoS attacks
- Set guidelines and expiration intervals for user passwords
- Trigger alerts that email you whenever a monitored event happens
- Use only FIPS 140-2 certified encryption algorithms
- Restrict users to certain directories and subfolders
- Generate audit logs of all user events and file activity
- Encrypt files on disk using AES-256 encryption
4. It can Secure and Automate Your File Transfers
Ad hoc file transfers can chip away at important development time, especially if they’re created and executed manually. Eliminate that frustration with GoAnywhere. Transfer files to trading partners, customers, and internal servers through workflows (projects), then schedule them to run at certain dates and times using a built-in scheduler or existing scheduler software.
No need to worry about the security of the data you’re transferring, either. Every file can be secured using various encryption methods, depending on your preferences and setup. You can encrypt file transfers over AS2, FTPS, and HTTPS using SSL or SFTP and SCP using SSH. GoAnywhere also uses Open PGP and GPG for encrypting and decrypting files with public/private keys.
5. It Seamlessly Integrates with CL, RPG, and COBOL Programs
The GoAnywhere command, RUNPROJECT, can be entered on any command line, run from CL/RPG/COBOL programs, or run from job schedulers. Executing this command allows a single install of GoAnywhere to execute and manage all the file transfer needs within an environment.
6. It Supports the use of IBM i Commands
The sky’s the limit with GoAnywhere, and use of IBM i commands in the product are no exception.
Don’t want to switch back and forth between GoAnywhere and your IBM i console? Execute IBM i commands and programs through a GoAnywhere connection with an IBM i server. Up to 35 parameters can be used to pass variables and constant values to the program, and commands are included for performing Open PGP encryption and decryption, SFTP transfers, ZIP compression, and more.
7. It Runs Triggers to Process Files Whenever They’re Uploaded or Downloaded
Enhance your productivity on your IBM i systems with GoAnywhere’s triggers. Triggers can be defined to monitor for and react to certain events, such as when a file is uploaded or downloaded by a trading partner. They can also run a variety of processes. For example, with triggers you can:
- Send an email to an employee when a file is uploaded by a trading partner
- Move a downloaded file into an archive folder
- Run an executable file, batch file, or shell script to process an uploaded file
- Remove an unsuccessful file upload from the folder
- Call a project to decrypt and import a newly uploaded file’s contents into a database table
8. It can Restrict Users to Specific IFS Folders
If you don’t want users (or groups of users) to have access to certain areas on the IBM i, GoAnywhere can help you confine users and groups to specific IFS folders and directories. You can also give users granular permissions and disk quotas, which limits storage space usage for each user and folder.
9. It can Help You Meet Several Compliance Regulations
Most organizations need to be compliant with a variety of industry security standards, including PCI DSS, HIPAA, the GDPR, GLBA, FISMA, and state regulations. Without the right solutions and policies, gathering the data you need and creating audit reports can add hundreds of hours to an IT team’s workload.
GoAnywhere helps meet compliance requirements on the IBM i in several ways. You can learn more about each compliance standard and regulation, and how GoAnywhere helps address each one, on this page: Data Security Compliance for File Transfers.
10. It Secures Files at Rest with Open PGP and AES-256 Encryption
It’s not enough to secure files in transit. In order to meet strict compliance requirements for PCI DSS, HIPAA, and more, data should be protected at rest to minimize vulnerabilities and risk of data loss. GoAnywhere addresses the privacy and integrity of sensitive information with Open PGP for IBM i. It also secures folders using AES-256 encryption, which automatically encrypts the data as it’s written or added to designated folders.
If you’re ready to learn more about GoAnywhere and the IBM i, this on-demand webinar might be for you. "IBM i Webinar: Simplify and Protect Your File Transfers" explores how GoAnywhere MFT works with the IBM i to streamline your file transfer and encryption practices, and our IBM i experts give viewers a detailed demonstration of the product.
This recording is packed with information. Don’t miss out; view the webinar here.
Learn more: Everything You Need to Know about PGP Encryption
