
Encryption is key to securing organizational data in the short term and long. However, there are a few different types of encryption that organizations can use to achieve the optimal level of security. GnuPG is one of the most notable. However, today we’ll break down how PGP encryption works and how to use it to maintain the safety of your files.
The Pros and Cons of PGP Encryption
PGP, otherwise known as Pretty Good Privacy, is used to encrypt and decrypt files and authenticate messages through the use of digital signatures. PGP can used for the purposes of encrypting emails and files as well as verifying message recipients. Essentially PGP encryption can be a very powerful tool for users. PGP encryption is essentially unbreakable and is used to secure private communications, making it a leading solution for cloud security.
However, there are some aspects of PGP encryption that might be seen as a hurdle for organizations to use. Here are some things to consider about PGP encryption:
PGP Encryption Hurdles
- Complexity: PGP encryption can be pretty complex so it takes time and effort to exchange complicated messages between users. Some employee training may be required. However, secure MFT solutions like GoAnywhere make it as easy as possible for users to employ PGP encryption.
- Key Management: It’s important to understand key management in order to avoid incorrectly using, losing or corrupting PGP keys. If done incorrectly, other users within the organizations as well as vendors and trade partners will be put at risk. Just make sure that users are using PGPs correctly.
Related Reading: Getting Started with GoAnywhere’s PGP Key Manager
How to Encrypt with PGP
PGP is complicated but can be easy to use once you get through the initial learning process. The process is guided by a few simple steps. So, how do you encrypt data using PGP encryption? Let’s break it down.
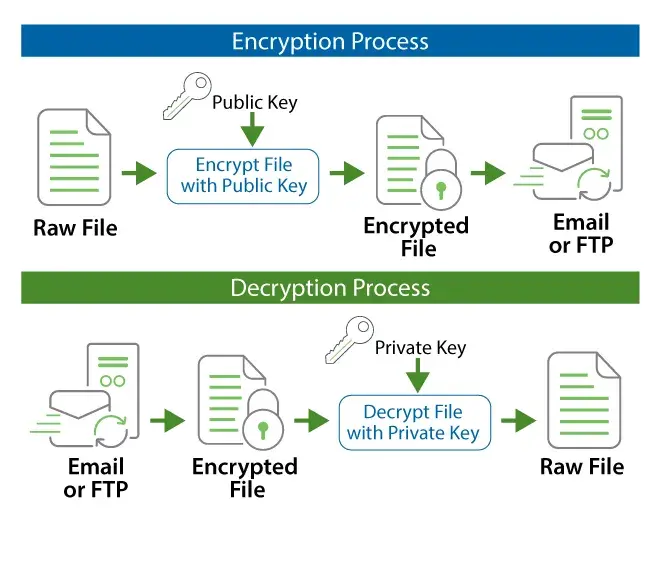
- The first step in encrypting data with PGP is to obtain your trading partner’s public key to encrypt a file. This key is not the same key that will allow the intended receiver of the message to decrypt the file for viewing and/or editing.
- Once you’ve obtained the key, users can import the public key to a key vault. Once the key has been imported to the key vault, users should then create a project within the software that will be used to encrypt the file/data that you need secured in motion and at rest. In many instances, users will be prompted to sign the file with a private key which adds another layer of security to the data in question.
- Users should always double check that the project has been set up to properly encrypt and secure the data, they can execute the encryption process and exchange data safely between stakeholders.
PGP lets users encrypt, decrypt, sign and verify files from their PCs or workstations. An integrated key manager allows anyone to quickly create, import, export and manage PGP keys needed to encrypt and decrypt files. Best of all, it's intuitive so users can confidently use GoAnywhere’s PGP software.
Raise the Security Level of Your Organization with Open PGP
GoAnywhere MFT provides an easy-to-use and secure way to exchange files between stakeholders.
