Take your secure file transfers to the next level. Seamlessly integrate managed file transfer with advanced threat protection and adaptive data loss prevention to keep your sensitive data secure. The SFT Threat Protection bundle from Fortra allows you to collaborate safely without malware entering your organization, or employees losing or mishandling data.
What Is the SFT Threat Protection Bundle?
Sharing information comes with inherent risks. There’s the risk of opening your systems to threats, such as malware or even threats hidden within file transfers. There’s the risk of exposing the wrong content, whether sent by mistake or hidden in metadata. GoAnywhere MFT offers award-winning threat protection and data loss prevention (DLP) across email, web, and endpoints to strengthen your data security.
What Can You Do With The Threat Protection Bundle?
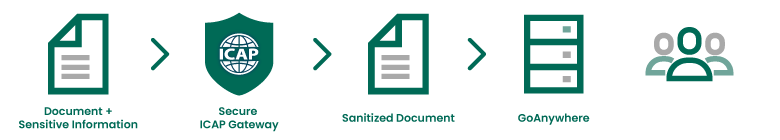
The SFT Threat Protection bundle allows you to inspect managed file transfer content for threats as well as leakage. A smooth integration between GoAnywhere MFT and the Clearswift Secure ICAP Gateway makes this possible, featuring:
- Anti-virus and malware protection
- Deep content inspection
- Adaptive data loss prevention
- Media type protection
Here are three common ways you could use this integration to enhance your file transfer security.
Prevent Files with Malware from Being Shared
Simply check a box in GoAnywhere to turn on easy anti-virus protection through the Secure ICAP Gateway to scan all inbound file transfers.
Detect and automatically strip out active content like embedded malware, triggered executables, scripts, or macros used to extract or hold sensitive data hostage. Advanced Threat Protection sanitizes—without delay in delivery—as only the malicious active content is removed, allowing the file transfer to continue unhindered.
This morph-free protection guards against today's leading malware and ransomware (i.e. CryptoLocker, CryptoWall, TorrentLocker, Dridex Dyre, BlackEnergy, etc.) and tomorrow's even more sophisticated threat variants.
Block Files with Sensitive Data From Being Shared
Prevent files with PII or other sensitive data from being transferred. GoAnywhere Threat Protection can inspect file contents, then stop and block files from being shared based on policy.
Redact Sensitive Information from File Transfers
Ensure sensitive data is not transmitted OR received — whether by:
- Detecting or removing geotags, document properties, email addresses, or other metadata from documents
- Replace sensitive text—including PII, PCI, and HIPAA—with asterisks
- Detecting and removing text contained in scanned images with Optical Character Recognition (OCR)
- Detecting and removing offending content with text redaction
How SFT and Secure ICAP Gateway Keep Government Services Secure
When a large government agency needed to help its citizens submit forms for building permits, pay fees, and report crimes remotely due to the COVID-19 pandemic, they turned to integrated security solutions from Fortra. They already used GoAnywhere for file transfers and added the solutions’ Secure Forms capabilities to help keep the wheels of government rolling. Incorporating data loss prevention and threat protection provided by Clearswift Secure ICAP Gateway they gained additional layer of automated security and helped ensure the data citizens are uploading is safe and free of malware, viruses, or hidden metadata.
But Isn't Encryption Enough?
Encrypting sensitive file transfers is vital for ensuring the privacy and integrity of your data and complying with PCI DSS, privacy laws, and government regulations like HIPAA and Sarbanes-Oxley. Encryption can protect your files, but you can do more to ensure your messaging security. Stay aware of what is being transmitted—avoid transmitting viruses, malware, and advanced persistent threats.
Adding threat protection to GoAnywhere allows you to give some individuals the power to transmit PII, but not everyone. Even if your transmission process is secure, you may want or require the ability to audit who is sending what. The Secure ICAP Gateway enhances your encryption by limiting both who can transfer data, and what that data contains.
Two Leading Solutions, One Seamless Integration

The Clearswift Secure ICAP Gateway adds significant value to GoAnywhere MFT because of its threat protection, deep content inspection engine, adaptive data redaction, and flexible policy settings, while managed file transfer makes defining file movements a breeze.
Additional features you can add to your file transfer process are structural sanitization, document sanitization, data redaction, anti-steganography, and optical character recognition. Get the best and most thorough security for file transfer.
How Else Can Clearswift Help You?
Integrating Clearswift’s core ICAP Gateway and threat protection with SFT can resolve gaps in your process and provide additional benefits.
Audit and Control Data in File Transfers
Detect when customer, employee, or patient records in a file are uploaded to SFT, count the records, and maintain an audit log of what data was shared with whom. When you add Clearswift solutions to your SFT instance, you get Lexical Expression Qualifiers, which can detect records based on multi-field matches, and trigger different actions based on number of records detected (e.g., audit, refer to sender, redact, block).
Ensure You Accept the Correct File Types
If you need to accept specific types of files (multimedia, images, XML, Office, PDF), you can enforce "True type" file controls to ensure you don't receive binaries, executables, scripts, or other unwanted file types. Clearswift solutions defend your system based on file byte pattern rather than by name. Plus, the solution works with nested files over 50 levels deep.
See GoAnywhere Threat Protection in Action
GoAnywhere Threat Protection helps you share critical information inside and outside your organization with an unprecedented level of management control and security. We can show you how.